Advanced Data Protection
Enterprise grade security.
Built from the ground up.
Your business is nobody else’s.


Encrypted
Cloud Computing™
Our most advanced cloud security architecture specifically built with enterprise in mind.
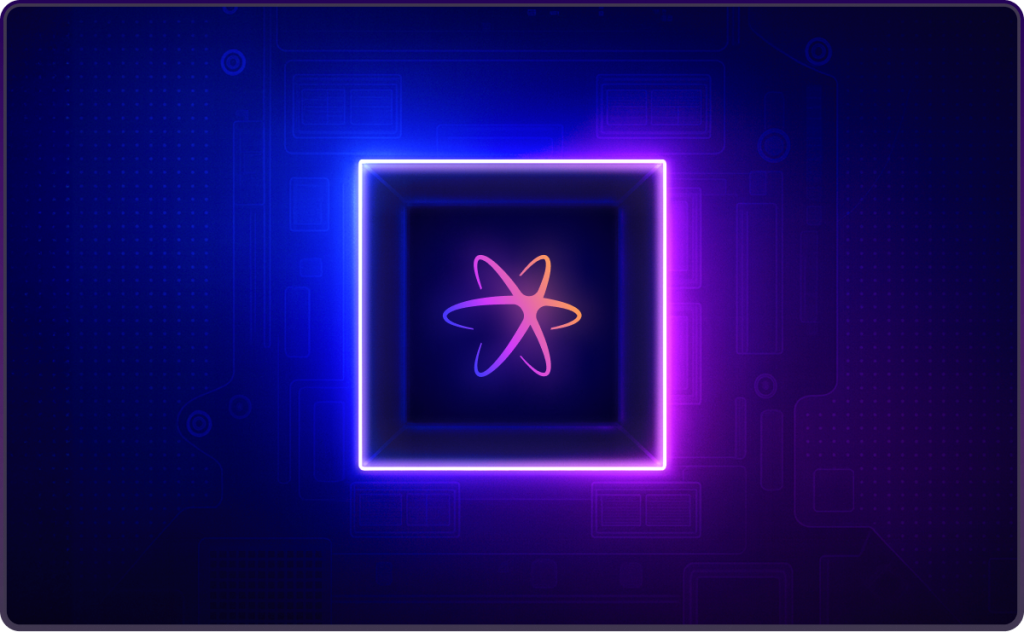
Encrypted Cloud Computing™
Cloud security at its highest.
Protections at its tightest.
DataTools has spent nearly three decades pushing the boundaries of what it means to turn your data quality from good to your greatest business asset. Always with an unwavering commitment to security, reliability, simplicity and unlimited support. As organisations rely on Seltaris to process massive address datasets in record time, they also trust us with some of their most sensitive information.
We achieved this once with the launch of Kleber in the Cloud, but we weren’t content to stop there. We set out to push these boundaries even further — with a goal to handle larger batch files securely with groundbreaking speed and performance.
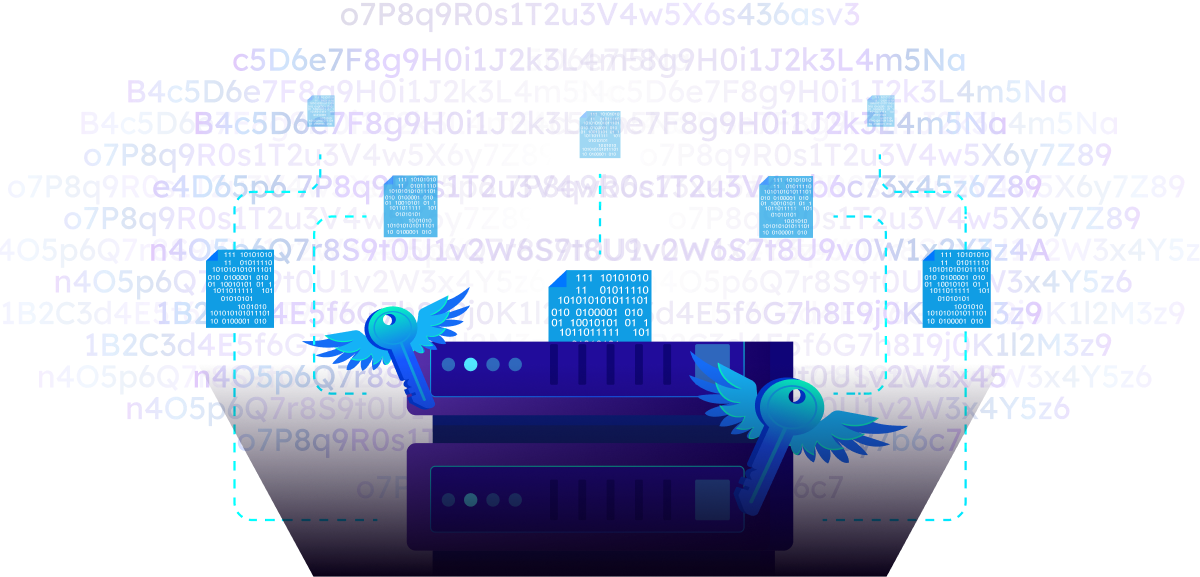
That led us to revisit our existing security stack and integrate additional layers for higher volume workloads. An innovative cloud security architecture purpose-built to process batch data securely at the scale today’s largest enterprises demand. We call it Encrypted Cloud Computing™.
Encrypted Cloud Computing™ builds on our robust, industry-leading cloud security, now taken to a whole new scale. It ensures that even the most intensive batch jobs run with airtight protections. Your data remains confidential, heavily encrypted, and not accessible to anyone.
Why we built it
Competing cloud environments, while convenient, pose familiar risks. Once data is inside competing cloud platforms, enforcing zero-access guarantees becomes challenging. Logging systems, privileged support consoles, and broad administrative access can inadvertently expose data or leave it vulnerable during operational troubleshooting.
That’s not acceptable for your businesses highly sensitive data. With Encrypted Cloud Computing™, we’ve taken a ground-up approach to cloud security that mirrors — and even surpasses — the standards we’ve long upheld with cloud and on-premise processing.
How it works with
Seltaris.
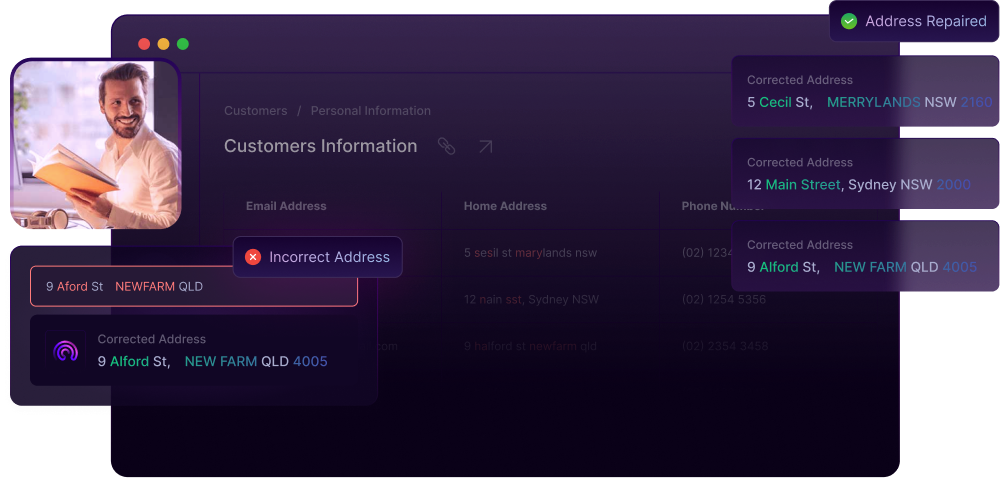
Seltaris is meticulously designed to protect your data at every step. Integrated into the core of our secure cloud environment, it utilises advanced encryption processes to handle your data without ever storing it unencrypted.
Thanks to Encrypted Cloud Computing™, we can securely process complex requests, ensuring that only you have access to your data. Your information remains encrypted during transit, throughout processing, and at rest, providing next-level security and peace of mind.
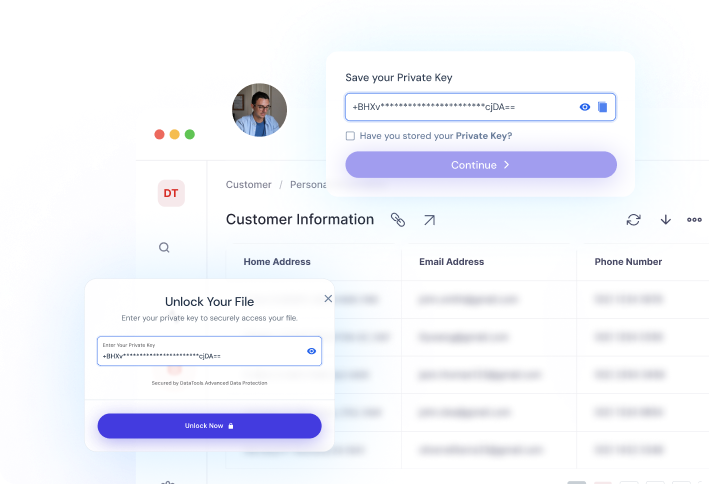
Before your Batch Process
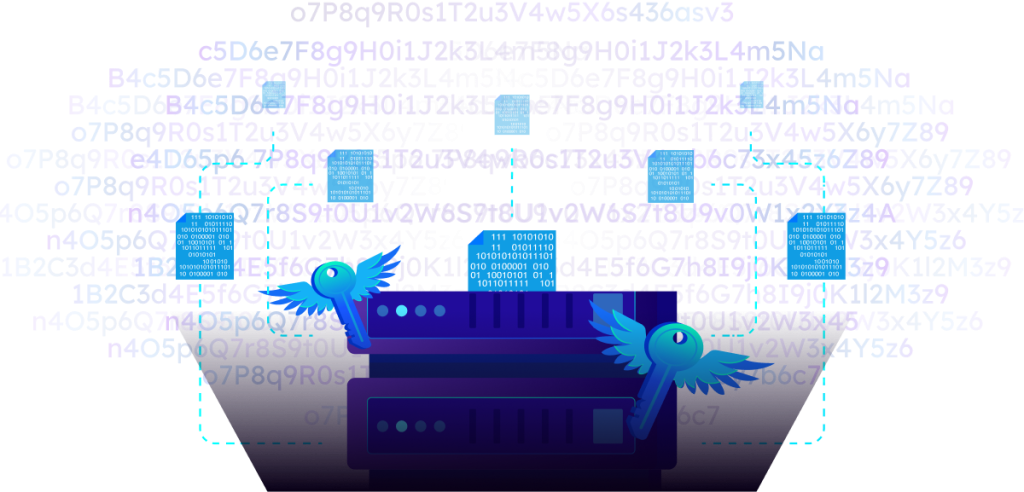
Before your batch process begins, we will provide you with a unique client secret key. This key is accessible only to you, the user; no one else, not even us internally, has access to this key. It is crucial to save this key securely, as it is the only means to access your file at the end of the job.

From the Client on Up
Once you begin the job, your data file (source file) is encrypted and transmitted from your client PC to our secure cloud environment via HTTPS, ensuring it remains protected during transit.

Data Uploading via DataTools Encryption Service
Once the initial records of your file enter our secure cloud environment, we begin importing the stream through our encryption service. This service is designed to encrypt each record individually, line by line, as it is being uploaded.

Secure Cloud Repository
After a record is encrypted, it is then transferred to our secure cloud repository. This continuous, record-by-record transfer ensures that the file is built up in the repository in real-time, without waiting for the entire upload to be completed. When the source file is fully present in our secure cloud repository, it is encrypted using an ephemeral key obtained from our identity server. This ephemeral key, along with the file, is designed to last only as long as the job.

The Splits
Time for Processing. The Altraservice
At lightning speeds, each file is sent to our Altraservice. This high-performance service decrypts each mini-encrypted file and processes its contents line by line in memory. Utilizing Human Touch technology, it validates and repairs each record. Once processing is complete, the record is re-encrypted and returned to the secure cloud repository.

Secure Key Management
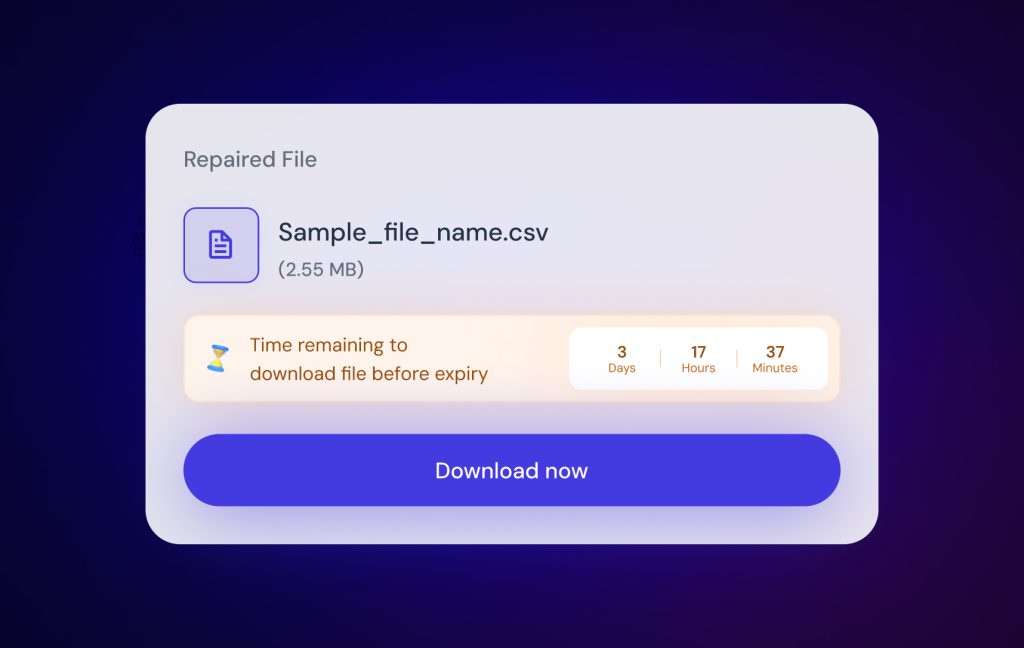
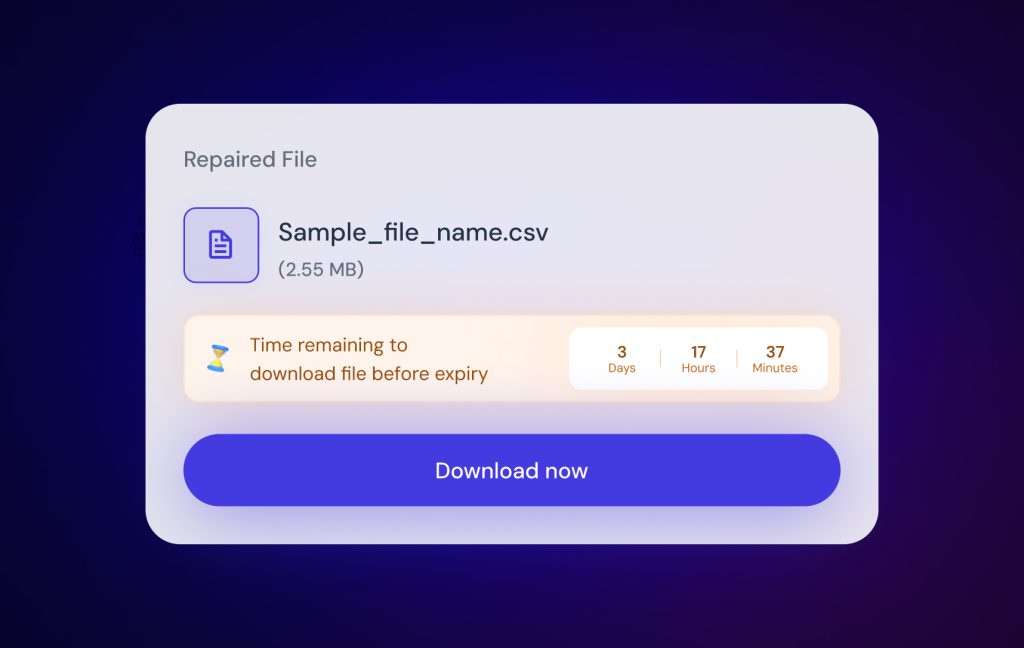
File Merging and Result Delivery
Governance

Private Keys
The single key to your encrypted result file.
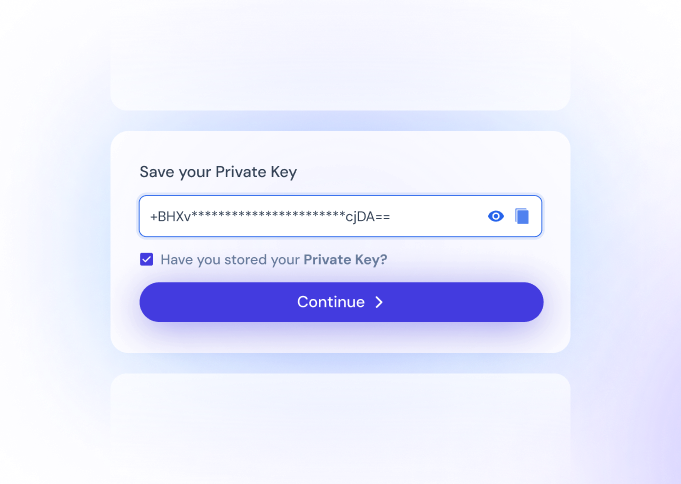
Control who sees.
A private key is your unique security credential, issued only to you, and it’s the one and only way to unlock your final result file.
When you begin a batch job, we generate a client secret key that is never shared, stored, or accessible by anyone else. From that point forward, every stage of your job relies on temporary, ephemeral keys managed through our secure identity servers. These working keys are used solely for in-memory processing and are destroyed the moment the job is complete. What remains is your encrypted result file, locked and waiting. Only your private key can decrypt it.
This design eliminates one of the biggest risks in traditional cloud environments: server-side access. On conventional servers, decrypted data can exist at rest, meaning administrators or third parties could potentially access your information.
By giving you sole control of your private key, Advanced data protection guarantees:
- Absolute ownership — You decide who can access your results.
- Enterprise grade security — Protections and security credentials specifically designed for the strictest compliance environments.
- Retention period — Once the retention period expires, the encrypted file is permanently erased from our severs.
There are no backdoors, no hidden access points, and no way for anyone else to step between you and your data. Even under force, we cannot hand over what it cannot see.
That’s DataTools.
Whenever data is involved,
security is rightly a concern.
Core Features
Explore the core features
of Seltaris
Human Touch™
The tool is innovative.
The experience is magical.
At the core of Seltaris lies our intuitive Human Touch Technology. This powerful software features large, highly capable intelligence models specifically tailored to read and process data as efficiently as humans do.
Altraservice™
Groundbreaking Performance.
Feel the need. The need for processing speed.
Our latest step in pushing the boundaries of batch processing data, this time in the direction of fast processing speeds.
Advanced Data Protection
Enterprise grade security.
Built from the ground up.
Seltaris is meticulously designed to protect your data at every step. Integrated into the core of our secure cloud environment, it utilises advanced encryption processes to handle your data without ever storing it unencrypted.
Design made simple
Innovation for all.
The best innovations are built for everyone.
We have always believed that data quality software should be simple.
Health Check Report
Data quality at its finest detail.
This Health Check Report delivers a clear and comprehensive assessment of your submitted address data delivered in an easy to read PDF, analysed through the Seltaris service.

Bulk Data Enhancement Tool
Seltaris
High Quality Results, Unbelievable Performance. Incredibly Secure.








